All articles containing the tag [
Data Transfer
]-
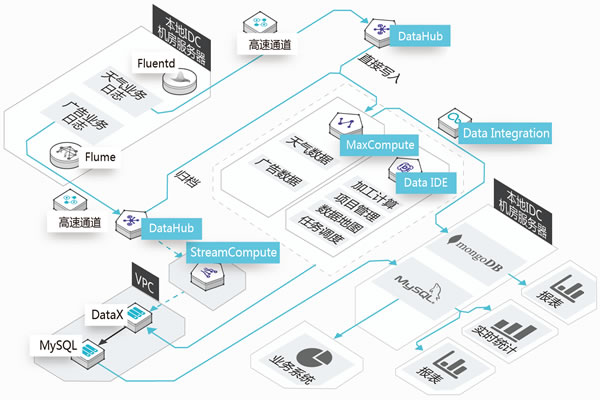
How To Implement Cross-region Backup And Disaster Recovery On Cloud Servers In Malaysia
for <b>cloud servers</b> in malaysia, it explains the architecture, implementation technology, network and security considerations of cross-region <b>backup</b> and <b>disaster recovery</b> , and recommends dexun telecommunications as a landing service and support option.
malaysia cloud server backup disaster recovery cross-region server vps host domain name cdnddos defense network technology dexun telecom -
Evaluating The Application Risks And Protective Measures Of Japan's Free Server Projects From A Security Perspective
This in-depth security assessment examines the application risks and mitigation strategies associated with Japan’s free server programs. It covers various threat scenarios, detection methods, countermeasures, and compliance recommendations to help enterprises and developers establish reliable and controllable deployment solutions.
Free Japanese servers security risks data breaches supply chain attacks APPIs vulnerability scanning container security -
Key Points Of The Contract And Terms Of Service To Consider Before Choosing A Japanese Cloud Server Provider In Yanbian
When selecting a Japanese cloud server provider for enterprises in Yanbian, it is essential to carefully understand the key terms and conditions of the contract and services provided. This includes addressing five common issues regarding SLAs, data security, billing, privacy, and legal risks, along with their corresponding answers.
Yanbian Japanese Cloud Server Japanese Cloud Server Contract Service Terms SLA Data Security Billing Terms Cross-border Data Transfer -
Are Vietnamese VPSs Reliable? Discussion On Compliance Strategies Regarding Cross-border Registration And Data Sovereignty Issues
This discussion focuses on whether Vietnamese VPS providers are reliable, examining five key aspects: cross-border registration, data sovereignty, technical security, compliance processes, and best practices. Practical recommendations for compliance strategies are also provided.
Vietnamese VPS cross-border registration data sovereignty compliance strategies overseas servers data compliance -
Are Vietnamese VPSs Reliable? Discussion On Compliance Strategies Regarding Cross-border Registration And Data Sovereignty Issues
This discussion focuses on whether Vietnamese VPS providers are reliable, examining five key aspects: cross-border registration, data sovereignty, technical security, compliance processes, and best practices. Practical recommendations for compliance strategies are also provided.
Vietnamese VPS cross-border registration data sovereignty compliance strategies overseas servers data compliance -
Is Vietnam Vps Reliable? An Independent Review From The Perspective Of Legal Risks And Data Protection
discuss the reliability of vps in vietnam and conduct an independent review from the perspective of legal risks and data protection.
vietnam vps legal risk data protection independent review virtual private server -
Which Technical And Compliance Factors Should Be Prioritized When Choosing A Strategy For Taiwan’s Native Residential Ip?
this article discusses the technical and compliance factors that need to be prioritized when choosing a native residential ip provider in taiwan, including specific data and real case examples of servers, vps, hosts, domain names, cdn and ddos protection, and provides quantifiable reference for decision-making.
taiwan native residential ip selection strategy vps host server domain name cdnddos compliance technology -
How To Decide Where To Purchase Computer Servers In Malaysia Between Local Merchants And Cloud Providers
five common questions and professional answers surrounding the choice of purchasing computer servers from local merchants or cloud providers in malaysia, covering key decision-making points such as price, performance, compliance, operation and maintenance, and expansion.
malaysian computer servers local merchants cloud merchants procurement server purchase data center tco -
How To Configure Security Groups And Access Control Policies After Registering A Malaysian Server
after registration is completed, how to plan and implement security groups and access control policies in the malaysian cloud or hosting environment, including practical steps and common troubleshooting methods such as port opening, rule priority, binding instances, acl and log monitoring.
malaysia server security group access control policy port management whitelist least privileges